Introduction
In an era of escalating geopolitical tensions, destructive cyber attacks—including wipers, ransomware variants, and data-destruction malware—pose a growing existential threat to organizations. While such attacks remain relatively rare due to the risk of retaliation, their impact can be catastrophic when they occur. This guide offers proactive, scalable hardening strategies to help organizations fortify their environments against not only outright destruction but also against the precursor activities of reconnaissance, privilege escalation, lateral movement, and persistence. The recommendations complement existing endpoint and network security tools, focusing on custom detection opportunities that surface anomalous behavior diverging from normal baselines.
Understanding Destructive Threats
Destructive malware aims to render systems inoperable, destroy data, or erase forensic evidence. Threat actors may deploy wipers, modified ransomware, or custom destructive tools to achieve strategic or tactical goals. When conflict erupts, cyber attacks become an inexpensive and easily deployable weapon, often resulting in a surge of incidents. Organizations must therefore adopt a posture of continuous readiness.
Organizational Resilience Beyond Technical Controls
While technical hardening is critical, resilience also depends on governance that integrates crisis preparation and orchestration. A "living" resilience posture incorporates two key elements:
Out-of-Band Incident Command and Communication
Establish a pre-validated, out-of-band communication platform that is completely decoupled from the corporate identity plane. This ensures that key stakeholders—including executives, incident responders, and third-party support teams—can coordinate and communicate securely even if primary systems (email, chat, video conferencing) are compromised or unavailable.
Defined Operational Contingency and Recovery Plans
Baseline operational requirements must include manual procedures for vital business functions to maintain continuity during restoration or rebuild efforts. Organizations should develop detailed playbooks that outline step-by-step recovery processes, data restoration priorities, and fallback mechanisms.
Technical Hardening and Proactive Defense
Hardening should focus on reducing the attack surface and implementing layered defenses. The following subsections detail actionable steps.
Access Control and Privilege Management
Implement strict access controls, following the principle of least privilege. Use just-in-time (JIT) access and privileged access workstations (PAWs). Regularly audit and remove dormant accounts. Ensure that administrative credentials are protected with multi-factor authentication (MFA) and are not shared.
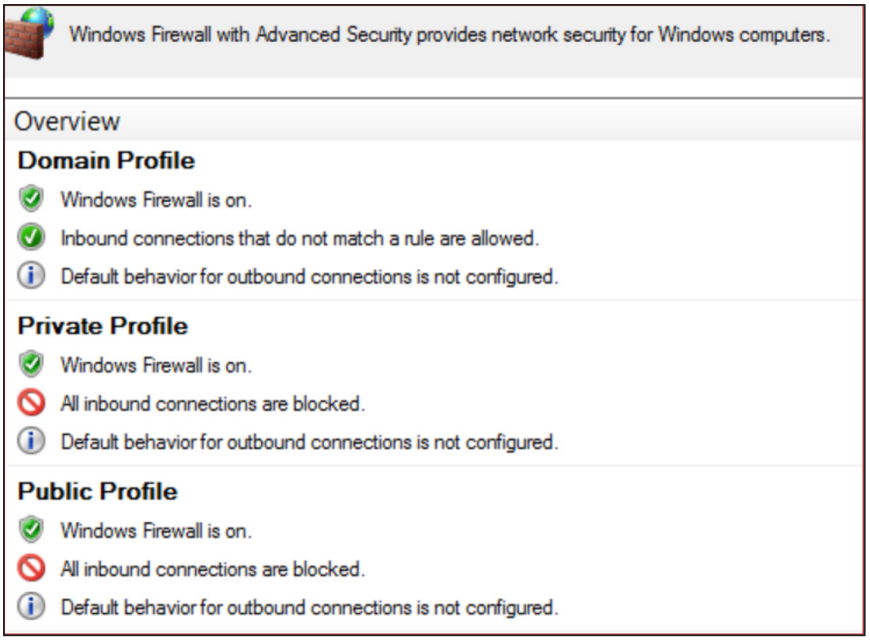
Endpoint and Network Security
Deploy advanced endpoint detection and response (EDR) solutions with behavior-based detection signatures. Use network segmentation to isolate critical assets and limit lateral movement. Enable logging across all systems, with centralized storage that is write-once, read-many (WORM) to prevent tampering.
Custom Detection Opportunities
Custom detection rules should be correlated to specific threat actor behaviors. For example: monitor for unusual volume of file deletions or modifications (indicative of wiper activity); detect mass renaming of files (common in ransomware); alert on anomalous Service Principal Name (SPN) queries or abnormal PowerShell execution. These rules complement existing signatures by surfacing deviations from established baselines.

Preventing and Mitigating Destructive Attacks
A multi-layered strategy reduces the likelihood and impact of destructive events.
Data Backup and Recovery
Maintain offline, immutable backups of all critical data. Test restoration procedures regularly. Use the 3-2-1 backup rule: three copies, on two different media, with one offsite. Ensure backups are not reachable from the production network to prevent encryption or deletion.
Identity and Authentication Hardening
Implement strong authentication policies, including MFA for all users, especially for cloud and remote access. Use conditional access policies to block risky sign-ins. Monitor for anomalous authentication attempts—such as impossible travel or brute-force patterns.
Incident Response and Recovery Exercises
Conduct tabletop exercises and full-scale simulations that include destructive scenarios. Validate communication channels, manual procedures, and restoration timelines. Update runbooks based on lessons learned.
Monitoring and Detection
Effective monitoring depends on understanding the organization’s unique environment. Security teams should establish pre-baselines of normal behavior to identify anomalies. Integrate custom detections into SIEM platforms and ensure alert triage workflows are well-defined.
Network Traffic Analysis
Monitor for unusual outbound traffic patterns, especially data exfiltration attempts. Detect command-and-control (C2) beaconing through DNS anomalies or abnormal connections to known malicious IPs. Use network detection and response (NDR) tools to inspect encrypted traffic where possible.
Endpoint Behavior Monitoring
Enable process auditing and file integrity monitoring. Watch for suspicious use of built-in tools like wmic, powershell, or mshta. Alert on attempts to disable security services or modify registry keys related to system hardening.
Conclusion
Destructive cyber attacks demand a proactive, holistic defense strategy that combines technical hardening, organizational resilience, and continuous monitoring. By implementing the recommendations outlined in this guide—ranging from out-of-band communications to custom detection rules—organizations can better protect their assets, maintain continuity, and recover swiftly when attacks occur. Preparation today prevents devastation tomorrow.