How HashiCorp Vault Addresses AI Agent Security Challenges
As organizations increasingly deploy autonomous AI agents across their environments, traditional identity and access management (IAM) systems—designed for predictable human users and workflows—fall short. AI agents are non-deterministic actors that require a fundamentally different authorization model: one that combines identity, delegation, runtime policy evaluation, and ephemeral authorization. HashiCorp Vault now introduces native support for AI agents with capabilities such as an agent registry, granular identity-based policies, and per-request (ephemeral) authorization. These features enforce guardrails, provide clear attribution, and standardize security across agentic workflows. Below, we answer common questions about this new approach.
Why do AI agents require a different authorization model compared to traditional IAM?
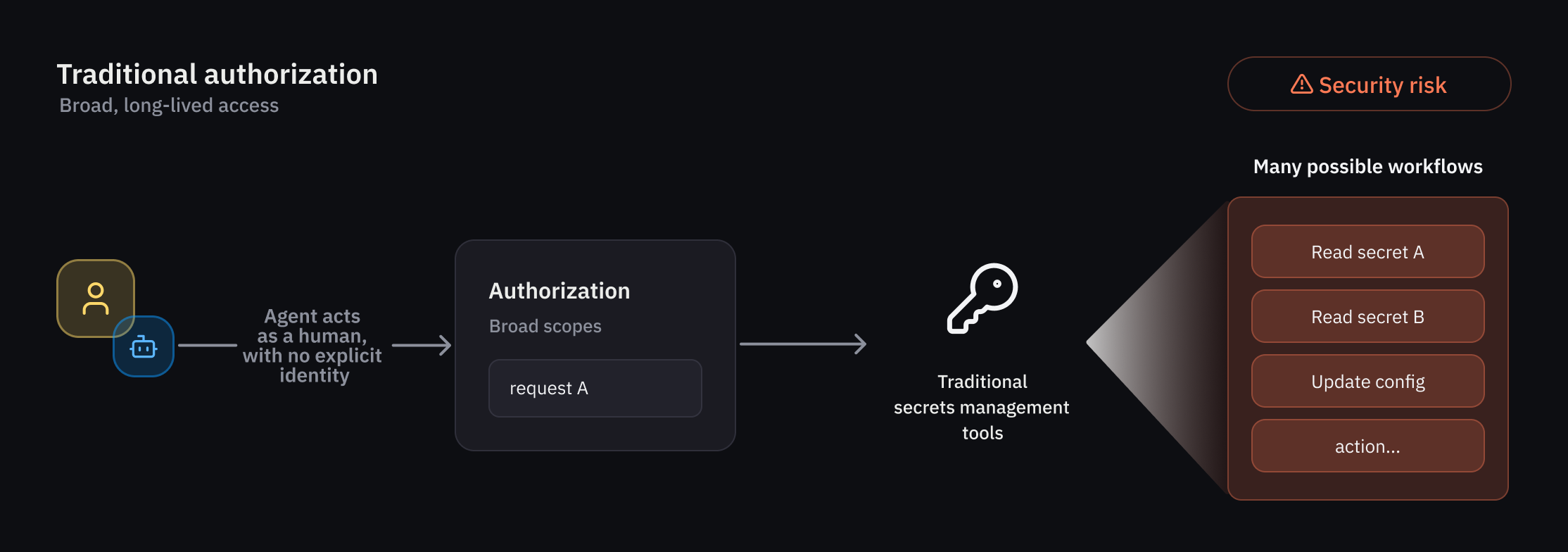
Traditional IAM assumes deterministic users and workflows—humans or machines that follow predictable patterns. AI agents are autonomous, non-deterministic actors that can make decisions on the fly, interact with multiple systems, and operate in delegation mode (acting on behalf of a human). This introduces unique risks: agents may take unpredictable actions, require temporary and highly scoped access, and need clear attribution for audit trails. Traditional static permissions and long-lived credentials are insufficient. Instead, AI agents need an authorization model that evaluates policies at runtime, grants ephemeral access tied to specific tasks, and explicitly tracks delegation from human users. Vault’s new capabilities—agent registry, identity-based policies, and per-request authorization—directly address these requirements by providing a dedicated framework for registration, authorization, credential management, and observability tailored to agentic workflows.
What are the key security challenges that AI agents introduce?
AI agents introduce several security challenges that differ from traditional non-human identities (NHIs) or human users:
- Unpredictability: Agents often operate in non-deterministic ways, making it hard to enforce static access controls. They may require guardrails that adapt to runtime context.
- Delegation and attribution: Agents frequently act on behalf of human users (on-behalf-of or OBO pattern). It becomes critical to trace which human authorized which agent action, and to ensure that delegation is explicitly recorded and consent-based.
- Fine-grained scoping: Because agents perform diverse tasks, they need access that is tightly scoped to specific actions, resources, and timeframes—not broad, long-lived permissions.
- Auditability: Organizations must be able to attribute every agent action to a specific identity (agent and human) for compliance and forensics.
- Cross-environment consistency: Agents operate across clouds, on-premises, and hybrid environments, requiring a standardized security approach.
Vault addresses these by treating agents as a separate identity type, enforcing deterministic guardrails on non-deterministic behavior, and providing ephemeral authorization that expires after a task or time window.
What is the agent registry in HashiCorp Vault and how does it help manage AI agents?
The agent registry is a new primitive in Vault that allows developers to register and manage AI agents as distinct identities—separate from human users or traditional NHIs. This provides agent-specific oversight, particularly important in delegation flows where an agent uses an on-behalf-of (OBO) pattern from a human user. The registry ensures that delegations are explicitly tracked with consent, forming the foundation for a dedicated framework of registration, authorization, credential management, and observability. For example, an agent can be registered with metadata linking it to the human who authorized its actions. This enables clear attribution and audit trails: every action performed by the agent is traceable to both the agent identity and the delegating human. The registry also streamlines policy enforcement and credential lifecycle management for agents, reducing the risk of misattribution or unauthorized delegation.
How does Vault enforce granular identity-based policies specifically for AI agents?
Vault enforces least-privilege access for AI agents through a rich set of policy-based runtime controls. Because agent behavior can be non-deterministic, Vault applies deterministic guardrails and per-request access control. Administrators define policies that specify exactly what actions an agent can perform, on which resources, under what conditions (e.g., time-bound, context-dependent). These policies are identity-based: each agent has a unique identity managed via the agent registry, and policies are attached directly to that identity. When the agent makes a request, Vault evaluates the policy at runtime, checking context such as the delegation chain (which human authorized this action), the agent’s role, and the requested resource. This ensures that even if an agent’s behavior varies, it never exceeds its authorized scope. Additionally, Vault can enforce consent-based delegation, so an agent cannot act on behalf of a human without explicit, audited approval.
What is per-request (ephemeral) authorization and why is it important for AI agents?
Per-request, or ephemeral authorization, grants temporary access rights that expire immediately after a specific task or time frame—rather than issuing long-lived credentials. For AI agents, this is critical because agents often operate autonomously and may handle sensitive data or critical systems. With ephemeral authorization, each agent request is individually evaluated and authorized; the credentials used are short-lived and automatically revoked once the task completes. This reduces the risk of credential misuse if an agent is compromised or misbehaves. It also aligns with the non-deterministic nature of agents: since you cannot predict every action, you can enforce security at the request level. Vault implements this by issuing time-bound tokens or secrets for each authorized action, and by integrating with runtime policy evaluation. Administrators can set maximum durations or tie credentials to completion signals. This approach also simplifies auditing, as each authorization event is recorded with precise scope and timing.
How does delegation (on-behalf-of patterns) work with agent identities in Vault?
AI agents frequently operate in delegation mode—acting on behalf of a human user using an on-behalf-of (OBO) pattern. In Vault, this is handled through explicit consent and tracking. When a human delegates authority to an agent, that delegation is recorded in the agent registry, linking the agent to the human identity. Vault then enforces that the agent’s actions are bound by the human’s permissions, plus any additional constraints defined in agent-specific policies. During each request, Vault evaluates trust across multiple dimensions: the agent’s identity, the delegated human identity, the consent status, and the runtime context (e.g., which task, what resource). This ensures that the agent cannot exceed the scope of what the human has authorized. All delegation events are audited, providing clear attribution. For example, if an agent accesses a secret to complete a task, the audit log shows both the agent’s identity and the human who delegated. This model supports complex workflows where multiple humans delegate to one agent, or vice versa, while maintaining security and compliance.
When will these new AI agent features be available in Vault?
Select customers are currently evaluating Vault’s native AI agent capabilities through an early access program. These features include the agent registry, granular identity-based policies, and per-request ephemeral authorization. Based on feedback, HashiCorp plans to release a public beta for a broader audience later this summer. The general availability timeline will be announced after the beta phase. Organizations interested in participating in the early access program can contact their HashiCorp account representative or apply through the Vault beta portal. Once available, these capabilities will be integrated into existing Vault deployments, allowing organizations to manage AI agent identities alongside human and traditional NHIs from a single platform. The goal is to provide a standardized, secure foundation for agentic workflows across environments.
Related Articles
- Predicting Egocentric Video with Full-Body Action Conditioning: The PEVA Approach
- HashiCorp Vault Introduces Native AI Agent Support with Ephemeral Authorization and Identity Registry
- How IDE-Native Search Boosted AI Agent Performance by 50%
- Leveraging Simulation to Overcome Limitations in High-Voltage Testing and Submarine Cable EM Analysis
- Understanding Claude's Dreaming Feature: How Anthropic's AI Reflects on Past Work
- Alaska’s Tracy Arm Fjord Records Second-Highest Tsunami in History After Massive Landslide
- Streamlining Python Development: VS Code's New Environments Extension
- The Paradox of Unknowability: Using Gödel's Incompleteness to Conceal Secrets